Behind the scenes of America’s public safety announcements lies a sophisticated and evolving web of threats—from AI-enabled cyber intrusions and supply-chain vulnerabilities to shadow operations in critical infrastructure. This article reveals “What Officials Are Hiding From You: America’s Newest Security Threat,” breaking down the hidden risks that impact your privacy, finances, and daily life, while offering practical steps to protect yourself.
What Is America’s Newest Security Threat—and Why You Haven’t Heard the Full Story
Many Americans assume the greatest risks to national security are bombs or traditional military invasions. The reality is far more subtle—and pervasive. According to the Office of the Director of National Intelligence’s 2025 Annual Threat Assessment, “Both state and non-state actors threaten U.S. citizens, the Homeland, and U.S. interests” through cyber, supply-chain, disinformation, and infrastructure attacks. (DNI.gov)
One of the most urgent threats is hidden: state-backed cyber groups infiltrating U.S. critical systems and lying dormant—what you don’t see is far more dangerous than what you do. For example, the FBI has documented state-sponsored hacking campaigns against U.S. supply chains, telecoms, and government networks attributed to Salt Typhoon. (CSIS.org)
Why haven’t you heard the full story? Because many of these operations are classified, pre-positioned, or masked as “routine maintenance” in public communications. Compartmentalization, secrecy, and information control mean everyday Americans are often left in the dark.
Why This Matters to You—Everyday Impacts of Hidden Threats
- Credit, identity, and finances: When cyber-espionage hits telecommunications networks or financial regulators, your data and identity become vulnerable. For instance, China-linked hackers infiltrated U.S. bank-regulator email systems. (CSIS.org)
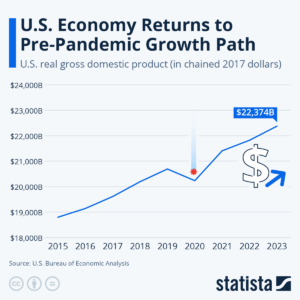
- Jobs, economy, and infrastructure: Hidden disruptions—such as delays in semiconductor supply chains—can result in job losses and higher consumer prices.
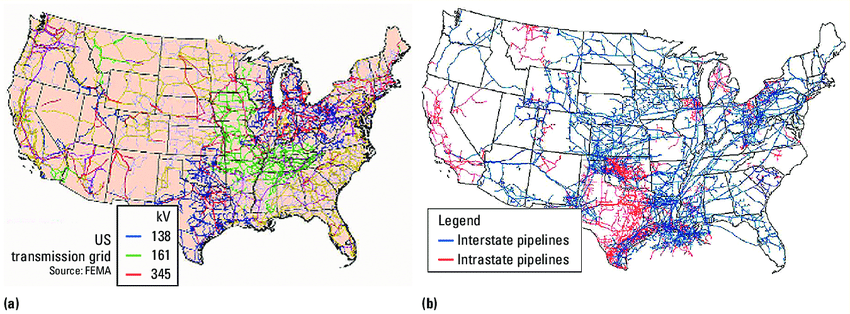
- Personal safety and planning: If your regional power grid or water-distribution system is compromised, your community may experience blackouts or water shortages. (DHS.gov)
- Trust and leadership: When vulnerabilities are undisclosed, public trust erodes, reducing the ability to prepare or protect oneself.
What Questions Are Americans Currently Asking—and the Answers You Need
1. What are officials hiding about cybersecurity threats to the U.S.?
Governments often withhold full breach details to avoid public panic, protect investigations, or prevent adversary advantage. For example, the Salt Typhoon campaign targeted U.S. telecom firms, but the breach was not fully disclosed until months later. (Wikipedia)
Takeaway: Be proactive—assume vulnerabilities exist and act accordingly.
2. How real is the threat from state-sponsored cyber actors targeting U.S. infrastructure?
Very real. The 2025 Annual Threat Assessment lists computer network attacks, economic coercion, supply-chain sabotage, and telecommunications infiltration as major threats. (DNI.gov)
Takeaway: Protect your digital footprint and ask employers/communities about infrastructure readiness.
3. Could my everyday data or devices be used against me or my community?
Yes. Hackers infiltrating networks may use customer data, control hardware, or create vulnerabilities that later activate.
Takeaway: Secure your devices, monitor personal data exposures, and enable two-factor authentication.
4. What is being done about supply-chain vulnerabilities and hidden threats?
Agencies like the Cybersecurity & Infrastructure Security Agency (CISA) issue alerts and guidelines, but corporate compliance varies. (CISA.gov)
Takeaway: If you rely on companies with global supply chains, ask about their security posture.
5. Are officials hiding foreign influence, espionage, or sleeper cells inside the U.S.?
Recent reports suggest yes—leaked memos indicate National Guard networks and state fusion centers were compromised. (Reuters)
Takeaway: Stay alert for community notices and ensure local authorities are transparent about risks.
6. Is disinformation or AI-generated content part of the hidden threat?
Absolutely. Adversaries use AI to produce fake content, deepfakes, and phishing campaigns aimed at American institutions. (APNews)
Takeaway: Verify official communications and approach online content skeptically.
7. How can individuals protect themselves if much of the threat is hidden?
While you can’t stop state-level threats alone, you can:
- Secure personal devices and networks
- Use encrypted communications and strong passwords
- Stay updated on cybersecurity alerts
- Diversify financial holdings
- Engage in community resilience planning
Takeaway: Preparedness boosts your resilience even without full knowledge.
8. How transparent are U.S. officials about hidden security risks?
Transparency is limited for national-security reasons, but some agencies publish summarized reports like the Homeland Threat Assessment.
Takeaway: Use public reports but recognize that unseen threats are often classified.
9. Could these hidden threats trigger major disruptions soon?
Yes. Many vulnerabilities are latent, waiting for a trigger or escalation.
Takeaway: Don’t assume “no news” means “no risk.”
10. What should I ask from my local/state authorities about hidden threats?
Ask about:
- State and local cyber-resilience plans
- Updates on critical infrastructure protection
- Community alerts on vulnerabilities
- Breach disclosure policies
Takeaway: Civic engagement improves your local security posture.
Trending FAQ: 10 Popular Search Queries (and Answers)
Q1: What “hidden threats” are U.S. officials not telling the public?
Many involve infrastructure infiltration, supply chains, telecom networks, and dormant malware campaigns.
Q2: Is U.S. infrastructure already compromised by foreign hackers?
Yes—state-sponsored campaigns have penetrated networks including telecoms, financial regulators, and cyber-fusion centers. (CSIS.org)
Q3: Are AI-generated cyberattacks a serious threat?
Extremely serious—AI is used to craft phishing, deepfakes, and deception campaigns. (APNews)
Q4: Why don’t agencies reveal breaches immediately?
To prevent panic, protect intelligence methods, and avoid adversary advantage.
Q5: What can ordinary citizens do if threats are hidden at national-security level?
Focus on personal cybersecurity, financial resilience, and local community preparedness.
Q6: Are local/state agencies doing enough to protect against hidden threats?
Not always—resource gaps and coordination challenges remain. (DHS.gov)
Q7: Could a hidden threat cause a nationwide blackout?
Yes—attacks on power grids, telecoms, or water systems are considered credible.
Q8: How will hidden security threats affect my job, data, or privacy?
If networks you rely on are compromised, it could mean service disruptions, data leaks, or identity theft.
Q9: Is the private sector involved in downplaying threats?
Often yes—companies may avoid disclosing vulnerabilities for legal or strategic reasons.
Q10: What are the signs a hidden threat has materialized locally?
Sudden service outages, quietly reported data breaches, unusual network activity, or unexplained disturbances.
Real-Life Examples
- In December 2024, the U.S. Treasury acknowledged a hack by China-backed actors accessing unclassified documents—details were withheld. (Wikipedia)
- The National Guard network was extensively hacked by Salt Typhoon between March–December 2024. (Reuters)
- Hackers used U.S.-based routers to target energy and water sectors under the guise of “routine” network access. (Justice.gov)
Practical Advice: What You Can Do Now
Indicators to monitor:
- Service interruptions or outages
- Leaks or hacks involving infrastructure or telecoms
- Alerts from CISA or DHS
- Local cybersecurity audits
Actions you can take:
- Secure devices with strong passwords and 2FA
- Protect identity: monitor credit reports
- Diversify data and finances
- Engage with community resilience efforts
- Support transparency: encourage vulnerability disclosure
Final Thought
The most dangerous threats are often invisible. Hidden cyber-espionage campaigns, supply-chain infiltration, and dormant infrastructure risks may not make headlines—but they affect your data, finances, and security. Officials may not reveal every detail, but staying informed, securing your digital life, and engaging with your community shifts you from reactive to proactive. Preparedness, awareness, and action are your best defense